Account Takeover Attacks Predicted to Increase in 2022
CyberEdge Group just released the 2022 Cyberthreat Defense Report, an annual survey of 1200 IT security professionals in 17 countries across 19 industries. The report presents critical insights into the top threats that online organizations are facing and their plans to protect their web and mobile apps and APIs. Here are four key takeaways.
1. Credential Stuffing and Account Takeover on the Rise
Respondents’ concern of account takeover (ATO) and credential stuffing attacks rose significantly this year. According to CyberEdge, “ATO attacks are poised to overtake malware as the #1 concern Malware is still perceived as the most important threat, but ATO and credential abuse attacks moved up from fourth place last year to #2 this year.”
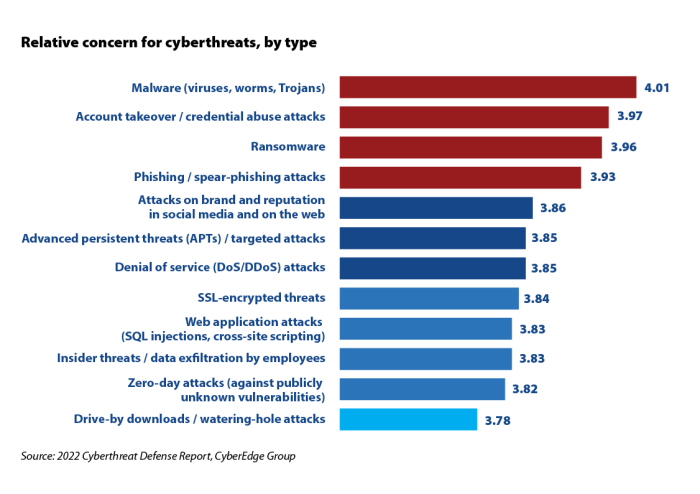
Concern for ATO and #credential stuffing attacks increased the most of any of the 12 cyberthreat categories in the survey. CyberEdge predicts that “ATO will take over the top spot in the next year or two.”
Protect Against ATO and Credential Stuffing Attacks:
- Proactively monitor compromised credentials actively being used in real-world attacks, and automatically disallow them from being used on your site.
- Leverage hidden and behind-the-scenes detection methods, such as honeypots and proof or work.
- Adopt machine learning technology to detect and mitigate automated login attacks against your web and mobile apps and APIs.


