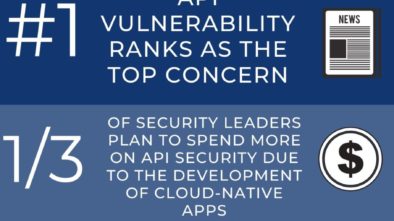
Enterprise Strategy Group Study Finds Very Few Companies Are Securing the Majority of Their Cloud-Native Apps With DevSecOps Practices | Business | valdostadailytimes.com
“ESG’s industry report is aligned with what we’ve long suspected with organizations, and with what...